BLUF
Space systems, missile defense architectures, and classified mission environments face a cybersecurity problem that is broader than network defense. The real challenge is protecting tightly connected systems where ground infrastructure, data flows, software assurance, cross-domain transfer, supply chain integrity, and mission continuity all matter at once. In these environments, a cyber failure does not simply create downtime. It can degrade command confidence, disrupt warning and response timelines, and put national security outcomes at risk. That is exactly why organizations need partners who understand secure engineering, federal compliance, operational tempo, and the reality of high-consequence missions.
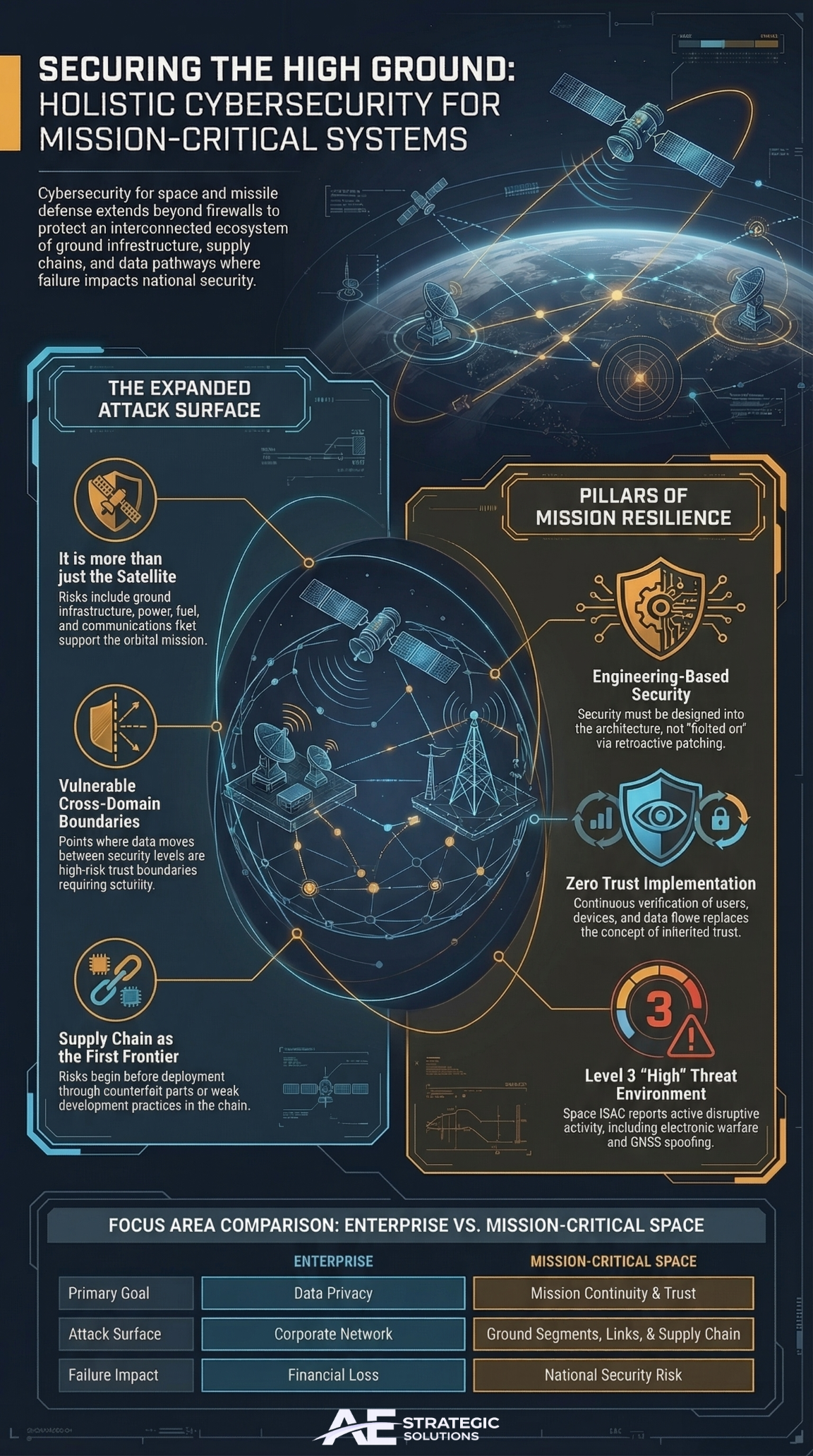
Table of Contents
- Why these mission environments are different
- The attack surface is larger than most people think
- Space systems face a persistent and active threat environment
- Missile defense depends on resilience, availability, and trust
- Classified systems bring boundary and data transfer risk
- Supply chain weakness can undermine mission assurance
- Secure engineering matters more than retroactive patching
- What federal leaders and primes should demand from partners
- Why this matters for AE Strategic Solutions
- Summary
- References
Why these mission environments are different
I view space, missile defense, and classified mission systems as some of the most demanding cybersecurity environments in government. They operate under pressure, connect multiple technologies and security domains, and support decisions that matter when time, trust, and continuity are at stake. This is not ordinary enterprise security work. These systems must remain dependable even when threat actors target data, communications, credentials, software, infrastructure, and operators at the same time. NIST guidance on trustworthy secure systems makes this point clearly by emphasizing defensible and survivable systems across machine, physical, and human components throughout the system life cycle.
That distinction matters because many organizations still talk about cyber risk as if the problem begins and ends with perimeter defense. It does not. In high-consequence federal environments, cyber risk spans design, integration, deployment, sustainment, and interconnection. The Space Force has also emphasized a more data-driven, AI-enabled force, meaning protecting data, models, decision support, and mission systems as a whole rather than as separate stovepipes.
The attack surface is larger than most people think
It is not only the platform
When people hear “space cybersecurity,” they often think only of the satellite. When they hear missile defense, they often think only about the interceptor or radar. In practice, the mission depends on a much broader ecosystem that includes ground segments, power, fuel, communications, identity, software updates, remote access, data pipelines, and mission support infrastructure. A senior Pentagon official said it plainly in 2025: if the power, water, or fuel that supports a space system ground segment is shut down, the result is a static display, not a functioning mission system.
That reality changes how leaders should think about security. The attack surface includes:
Ground infrastructure
Ground systems often carry the operational burden for control, telemetry, mission planning, and processing. If they fail, the mission can stall even if the platform itself remains intact. NASA’s 2025 GAO review stated that spacecraft and space systems operate in a cyber-threat environment, with increased risks of attack and mission disruption.
Data pathways
Mission data must move across systems, organizations, and classifications without losing integrity or confidentiality. That is difficult in any environment and even harder in classified ecosystems.
Cross domain boundaries
NIST defines a cross-domain solution as a controlled interface that allows manual or automatic access and transfer of information between different security domains. That makes these transfer points essential but also sensitive because they sit directly on mission-critical trust boundaries.
Sustainment and integration layers
Updates, patches, replacements, new software loads, and maintenance actions can all create opportunity for error or compromise if not tightly governed.
Space systems face a persistent and active threat environment
The threat is current, not theoretical
The threat environment for space related systems is active and evolving. In July 2025, Space ISAC assessed the threat environment for the space sector at Level 3 High and described disruptive cyber activity, electronic warfare, increased targeting tied to geopolitical conflict, social engineering tactics, and growing concern around GNSS interference, jamming, and spoofing. It also urged organizations to review credential access, scan for malicious traffic, patch critical systems, and lower reporting thresholds.
The concern is not limited to industry reporting. GAO reported in June 2025 that space systems are operating in an environment with increased risks of attack and mission disruption. That finding reinforces what mission leaders already know: cyber resilience for space systems must cover both the orbital mission and the terrestrial support architecture.
Data and AI introduce new dependencies
The Space Force FY 2025 Data and Artificial Intelligence Strategic Action Plan reflects a push toward becoming more data driven and AI enabled. That creates opportunity, but it also increases dependency on trusted data, secure data handling, model integrity, and resilient digital infrastructure. In other words, as decision cycles accelerate, the cost of corrupted data, degraded access, or manipulated feeds rises with it.
Missile defense depends on resilience, availability, and trust
Missile defense systems cannot afford ambiguous data
Missile defense systems exist to detect, track, assess, and support response under strict time pressure. A cyber event in this environment can affect availability, reliability, data integrity, communications, or sustainment. The Missile Defense Agency FY 2026 budget materials show continued support for operational systems including Aegis Weapon System, Ground Based Midcourse Defense, missile defense radars, and Terminal High Altitude Area Defense, along with funding to improve reliability, availability, and maintainability. That alone highlights the operational importance of resilient supporting systems.
From a cyber perspective, the challenge is not simply preventing intrusion. It is maintaining confidence that the system is functioning correctly when every second matters. If a mission system produces delayed, incomplete, manipulated, or mistrusted data, the downstream impact can be operationally severe.
Zero trust has direct relevance here
The Department of Defense Zero Trust Reference Architecture describes a data centric strategy that embeds security principles throughout the architecture to protect data and service operations while preventing, detecting, responding to, and recovering from malicious activity. In missile defense and related mission systems, that approach is not abstract doctrine. It supports the basic need to verify users, devices, workloads, and data flows continuously instead of relying on inherited trust.
Classified systems bring boundary and data transfer risk
Classified environments are not simple closed worlds
Some people assume a classified mission environment is secure because it is isolated. That assumption misses the real challenge. Classified systems still require people, updates, workflows, controlled movement of information, external dependencies, and interconnections with other systems or enclaves. Each of those can introduce risk if not engineered and governed carefully.
NIST’s Risk Management Framework explains that federal systems need structured lifecycle security and privacy management, while also noting that national security systems involve additional authorities and policy considerations. That combination means organizations cannot treat security as a one time accreditation event. They must sustain it through continuous monitoring, documented control implementation, and disciplined operational change.
Cross domain transfers deserve special scrutiny
Cross domain transfer is one of the most sensitive areas in classified missions. A cross domain solution exists specifically to move information between different security domains in a controlled manner. That function is necessary in many mission environments, but it also means security teams must pay close attention to rules, validation, integrity checks, identity, and operational governance at the boundary itself.
Supply chain weakness can undermine mission assurance
Cybersecurity starts before deployment
One of the biggest mistakes in federal mission systems is treating cybersecurity as something that starts after deployment. NIST SP 800 161 Rev. 1 warns that organizations face risk from products and services that may contain malicious functionality, may be counterfeit, or may be vulnerable because of weak manufacturing and development practices in the supply chain. It also states that these risks are tied to reduced visibility into how technology is developed, integrated, and deployed.
That matters a great deal for space, missile defense, and classified mission systems because these environments rely on high trust hardware, software, integration, logistics, and sustainment chains. A supply chain weakness can show up as a compromised component, a hidden dependency, poor software assurance, an insecure update path, an undocumented substitution, or a weak vendor practice. By the time that issue is discovered in the field, the operational cost can be much higher than in a standard enterprise setting.
Secure engineering matters more than retroactive patching
Security must be designed into the system
NIST SP 800 160 stresses that engineering-based solutions are essential for managing complexity and building more defensible and survivable systems. I agree with that completely. In high-consequence mission systems, security has to be part of the architecture, requirements, integration, testing, and sustainment. It cannot be bolted on after the fact and expected to hold under pressure.
That means asking hard questions early:
- What happens if communications degrade?
- What happens if data provenance becomes uncertain?
- What happens if a supplier component cannot be trusted?
- What happens if a credential is compromised inside a critical mission workflow?
- What happens if a cross domain process fails closed or fails open at the wrong moment?
Organizations that answer those questions early are far more likely to build systems that can survive real world stress.
What federal leaders and primes should demand from partners
For programs operating in these environments, I believe leaders should expect more from cybersecurity partners.
Deep mission understanding
A useful partner must understand the consequences of system failure, the realities of operational tempo, and the way cyber risk affects mission performance.
Comfort with classified and controlled environments
The partner should understand boundary protection, controlled data handling, secure operations, and the discipline required in sensitive environments.
Strong compliance and engineering fluency
NIST 800 53, RMF, zero trust principles, CUI protection requirements, cross domain considerations, secure systems engineering, and supply chain risk all need to be part of the conversation. NIST SP 800 171 Rev. 3 states that protecting CUI in nonfederal systems can directly affect the federal government’s ability to conduct essential missions and functions.
Responsiveness under pressure
When the mission is sensitive, response time matters. Reporting, escalation, documentation, and disciplined communication all affect outcomes.
Ability to support assurance, not only operations
The right partner helps the program prove trustworthiness through evidence, process discipline, and defensible implementation.
Why this matters for AE Strategic Solutions
This topic sits directly in the lane where AE Strategic Solutions can establish authority. High-consequence environments do not need generic cyber talk. They need a partner who understands what it means to protect mission systems where failure carries operational and national security consequences.
That means speaking clearly about space system resilience, classified data handling, mission-critical infrastructure, supply chain risk, secure engineering, and trust across the system life cycle. It also means understanding that cybersecurity in these environments is not a standalone function. It is part of mission assurance. Based on current NIST, DoD, GAO, and sector reporting, that is the level of seriousness these environments demand.
Summary
The cybersecurity challenge facing space, missile defense, and classified mission systems is not just about stopping intrusions. It is about protecting trust, continuity, data integrity, and mission performance across complex systems operating under real-world consequences. These environments depend on resilient ground infrastructure, controlled cross-domain movement, secure engineering, disciplined sustainment, and strong supply chain assurance. Leaders who understand that reality will choose partners differently. They will look for mission awareness, depth of compliance, engineering maturity, and the ability to operate where cyber failure has strategic cost.
References
- Government Accountability Office. (2025, June 25). Cybersecurity: NASA needs to fully implement risk management (GAO 25 108138). U.S. Government Accountability Office. https://www.gao.gov/products/gao-25-108138
- National Institute of Standards and Technology. (2018). Risk management framework for information systems and organizations: A system life cycle approach for security and privacy (Special Publication 800 37, Rev. 2). U.S. Department of Commerce. https://csrc.nist.gov/pubs/sp/800/37/r2/final
- National Institute of Standards and Technology. (2022). Systems security engineering: Considerations for a multidisciplinary approach in the engineering of trustworthy secure systems (Special Publication 800 160, Vol. 1, Rev. 1). U.S. Department of Commerce. https://csrc.nist.gov/pubs/sp/800/160/v1/upd2/final
- National Institute of Standards and Technology. (2024). Cybersecurity supply chain risk management practices for systems and organizations (Special Publication 800 161, Rev. 1, Update 1). U.S. Department of Commerce. https://csrc.nist.gov/pubs/sp/800/161/r1/upd1/final
- National Institute of Standards and Technology. (2024). Protecting controlled unclassified information in nonfederal systems and organizations (Special Publication 800 171, Rev. 3). U.S. Department of Commerce. https://csrc.nist.gov/pubs/sp/800/171/r3/final
- National Institute of Standards and Technology. (n.d.). Cross domain solution. NIST Computer Security Resource Center Glossary. https://csrc.nist.gov/glossary/term/cross_domain_solution
- Space Information Sharing and Analysis Center. (2025, July 2). Space ISAC issues TLP: CLEAR public release on threat level assessment. https://spaceisac.org/space-isac-issues-tlp-clear-public-release-on-threat-level-assessment-4/
- U.S. Department of Defense. (2022). Department of Defense Zero Trust Reference Architecture, Version 2.0. Office of the DoD Chief Information Officer. https://dodcio.defense.gov/Portals/0/Documents/Library/%28U%29ZT_RA_v2.0%28U%29_Sep22.pdf
- U.S. Department of Defense. (2025, April 22). Senior Pentagon official says cyber warfare poses significant threat to joint force. https://www.defense.gov/News/News-Stories/Article/Article/4163237/senior-pentagon-official-says-cyber-warfare-poses-significant-threat-to-joint-f/
- U.S. Department of Defense, Office of the Under Secretary of Defense Comptroller. (2025). Fiscal Year 2026 budget justification: Operation and maintenance, Volume 1, Part 1. https://comptroller.defense.gov/Portals/45/Documents/defbudget/FY2026/budget_justification/pdfs/01_Operation_and_Maintenance/O_M_VOL_1_PART_1/OM_Volume1_Part1.pdf
- U.S. Space Force. (2025, March 19). Space Force publishes 2025 Data, AI strategic action plan. https://www.spaceforce.mil/news/article-display/article/4124351/space-force-publishes-2025-data-ai-strategic-action-plan/

