BLUF
Unmanaged edge devices create mission risk long before they trigger a visible cyber incident. Field-deployed devices, remote sensors, tactical systems, network appliances, and disconnected assets expand the attack surface when organizations lose visibility into what is deployed, where it is operating, what software it runs, and whether it is still trusted. In federal environments, the danger is not only compromise. It is degraded mission awareness, slower response, weak asset inventory, stale patching, and false confidence in systems that leaders believe they control but do not fully see. NIST, DoD, and CISA guidance all point in the same direction: security must follow the asset, not the location, and unsupported or unmanaged edge devices now pose a significant federal risk.
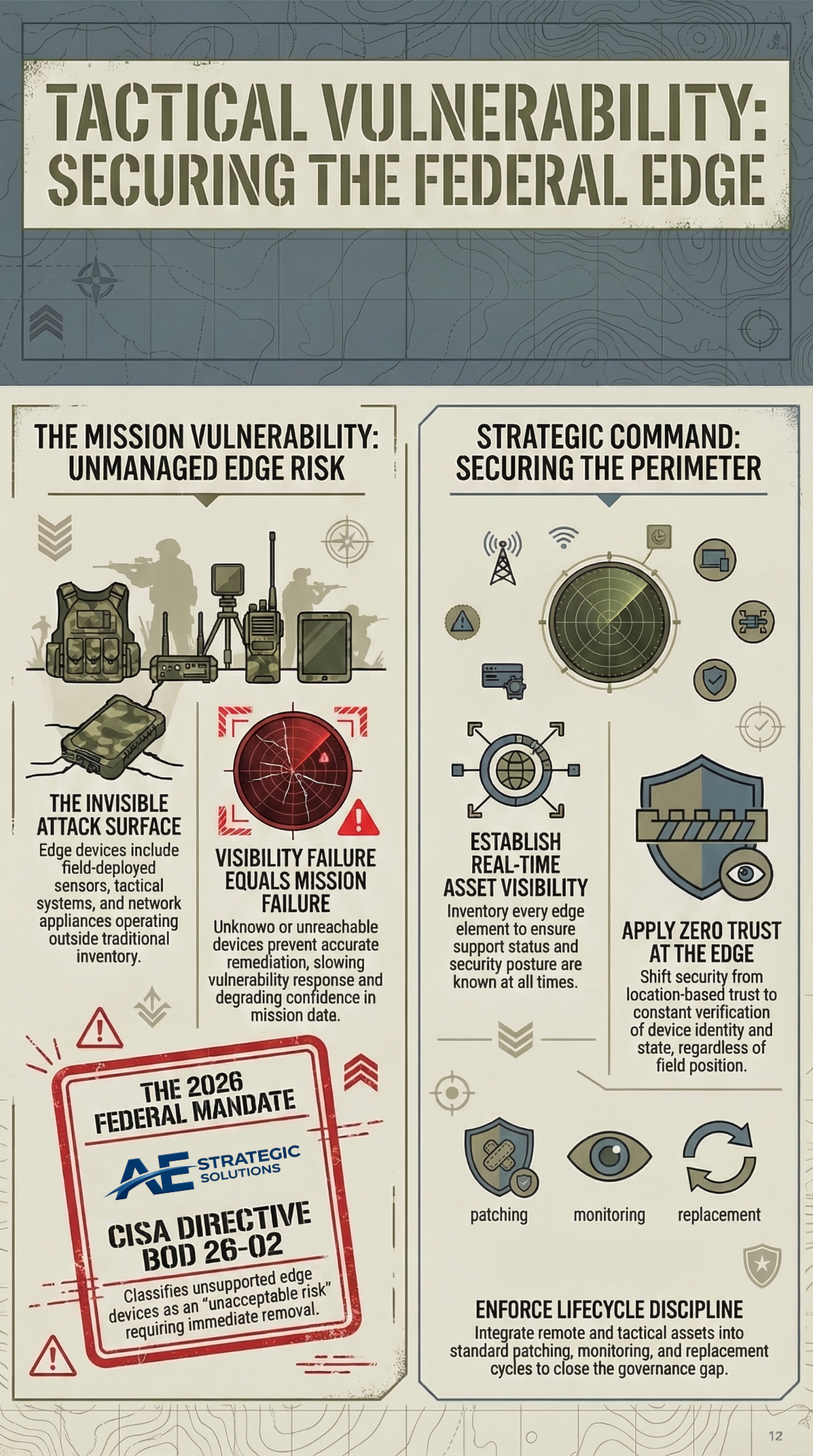
Table of Contents
- Why edge device risk is different
- What unmanaged edge devices look like in federal environments
- Why visibility failure becomes mission failure
- Disconnected and field deployed assets create control gaps
- Unsupported edge devices raise the federal risk floor
- Zero trust matters at the edge
- What federal leaders should do now
- Why this matters for AE Strategic Solutions
- Summary
- References
Why edge device risk is different
I see edge device risk as one of the easiest mission problems to underestimate. Many federal teams still think in terms of the core network, the data center, or the cloud environment. The problem is that the mission now extends far beyond those boundaries. It includes devices in the field, remote collection points, sensors, network appliances, gateways, tactical systems, and equipment operating with intermittent connectivity or in harsh conditions. NIST’s IoT guidance for the federal government makes clear that these devices are system elements and that adding them can change the system’s risk assessment and require additional or different controls.
That matters because edge devices are rarely passive. They sense, transmit, authenticate, route, store, and influence operational decisions. When they are unmanaged, the risk is not isolated to the device itself. It spreads into the system that depends on it.
What unmanaged edge devices look like in federal environments
Unmanaged edge risk is broader than one bad router or an old sensor left in the field.
In federal environments, it often includes remote sensors with weak update paths, tactical communications gear, fielded IoT devices, internet accessible network appliances, edge gateways, mobile collection systems, industrial or operational technology devices, and assets that fall outside normal inventory or patching routines. CISA’s current edge device guidance defines edge devices broadly enough to include firewalls, routers, switches, wireless access points, network security appliances, and IoT edge devices, while warning that unsupported devices create disproportionate and unacceptable risks to federal systems.
That is one of the core challenges. These assets often sit outside the places leaders naturally look first, but they still influence mission continuity and security.
Why visibility failure becomes mission failure
You cannot secure what you do not know well
The most dangerous edge devices are often not the most advanced. They are the ones teams forget, assume, or misclassify.
NIST Special Publication 800-207 states that zero trust shifts security away from static, network-based perimeters and toward users, assets, and resources, with no implicit trust granted based only on network location or ownership. The DoD Zero Trust Strategy reinforces the same idea by emphasizing responsibility for securing devices, applications, assets, and services across the enterprise. When an edge asset is invisible, stale, or outside the process, that model breaks down.
Visibility failure creates real mission effects:
Asset inventory becomes unreliable
If teams do not know exactly what is deployed, they cannot prioritize remediation or accurately assess exposure. CISA’s recent directive on end-of-support edge devices requires federal agencies to inventory, remove, and replace unsupported edge devices precisely because agencies need current visibility to reduce risk.
Vulnerability response slows down
A device that is unknown, unreachable, or poorly documented is hard to patch, isolate, or replace.
Trust decisions become weak
Leaders may assume a system is secure because the central environment is governed, while edge assets remain poorly understood.
Mission data becomes less dependable
If remote or tactical devices provide data to larger decision systems, loss of trust at the edge can degrade confidence across the mission chain.
Disconnected and field-deployed assets create control gaps
Field-deployed and intermittently connected devices introduce a different security reality. They may operate for long periods without direct administrative contact. They may depend on delayed updates, local operators, or constrained communications. NIST’s IoT guidance specifically notes that organizations are expected to manage system and organizational risk throughout the system development life cycle and that when IoT devices are introduced, often after the system is already operating, it is critical to consider the security impact of those changes.
This is where federal programs often get exposed. A device may be deployed with acceptable controls at day one, then drift over time as software ages, field conditions change, support contracts lapse, or new mission dependencies appear. Because the device is far from the core environment, weak controls are easier to miss and harder to correct.
That pattern is especially dangerous in tactical and operational settings, where teams may prioritize availability and mission speed under pressure. DoD’s OT zero-trust guidance underscores that control systems and operational environments require zero-trust implementation in addition to existing cybersecurity requirements, signaling that edge and operational assets cannot sit outside modern cyber discipline.
Unsupported edge devices raise the federal risk floor
CISA’s February 2026 directive and related fact sheet sharpen this issue considerably. CISA stated that end of support edge devices create disproportionate and unacceptable risks to federal systems because manufacturers no longer monitor them for defects or provide security patches and support. CISA also required Federal Civilian Executive Branch agencies to mature lifecycle management practices and use support status information to identify and remediate risk.
That is important for two reasons.
First, it confirms that edge device lifecycle failure is now treated as a federal governance problem, not merely a local IT issue. Second, it shows that unmanaged edge risk is not hypothetical or niche. It is current enough to drive binding federal action in 2026.
For mission owners, the lesson is direct. If an edge asset is unsupported, poorly inventoried, or outside the patch and monitoring cycle, it should be treated as a meaningful operational liability.
Zero trust matters at the edge
I think one of the most important mindset shifts here is simple: location should not equal trust.
NIST SP 800 207 explains that zero trust assumes no implicit trust based solely on physical or network location. The DoD Zero Trust Reference Architecture repeats that principle and applies it to both industrial and enterprise workflows. That matters because many edge environments still inherit old assumptions. If a device is deployed by the agency, mounted in the field, or connected through a mission network, teams may treat it as trusted by default. That is exactly the assumption zero trust is meant to break.
At the edge, zero trust is not only about access control. It is also about:
- verifying the device state
- maintaining accurate asset identity
- limiting unnecessary access and communications
- monitoring the device as part of the larger system
- refusing to assume that field location equals integrity
That is especially important when devices operate in remote, tactical, or operationally stressed environments.
What federal leaders should do now
Leaders do not need a slogan here. They need discipline.
Build and maintain real asset visibility
If the organization cannot say which edge devices exist, where they are, and what their support status is, it is operating at avoidable risk. CISA’s 2026 directive makes inventory and lifecycle visibility a concrete federal expectation.
Treat edge assets as system elements, not side components
NIST SP 800 213 makes clear that devices such as IoT assets are system elements whose inclusion can alter the system risk assessment.
Bring unsupported assets into a replacement plan
Unsupported edge devices should not linger because they are inconvenient to replace. CISA has already framed these devices as unacceptable federal risk.
Apply zero-trust principles to edge workflows
Trust should be based on verification, not proximity or ownership.
Close the gap between field deployment and cybersecurity governance
Remote and tactical assets should not live outside inventory, monitoring, patching, and decision processes simply because they are hard to reach.
Why this matters for AE Strategic Solutions
This is exactly the kind of problem AE Strategic Solutions should be talking about. Unmanaged edge device risk sits at the intersection of mission assurance, asset visibility, zero trust, lifecycle governance, and operational reality. It is not only a technical issue. It is a federal execution issue.
A credible partner in this space needs to understand how fielded assets affect compliance, cyber posture, and mission continuity over time. That means speaking clearly about device visibility, support status, risk assessment, disconnected operations, and the false confidence that comes from assuming deployed assets remain trustworthy after they leave the core environment.
Summary
Unmanaged edge devices pose hidden mission risk by expanding the attack surface exactly where visibility and control are weakest. Field-deployed devices, remote sensors, tactical systems, and disconnected assets can alter system risk, weaken inventory accuracy, slow remediation, and undermine trust in mission data when they are not governed as part of the full security environment. Federal guidance is moving in one direction: organizations must treat assets at the edge as real security dependencies, not peripheral conveniences. The leaders who understand that now will reduce risk before the hidden gap becomes an operational problem.
References
- Cybersecurity and Infrastructure Security Agency. (2026, February 5). BOD 26 02: Mitigating risk from end of support edge devices. https://www.cisa.gov/news-events/directives/bod-26-02-mitigating-risk-end-support-edge-devices
- Cybersecurity and Infrastructure Security Agency. (2026, February 5). CISA orders federal agencies to strengthen edge device security amid rising cyber threats. https://www.cisa.gov/news-events/news/cisa-orders-federal-agencies-strengthen-edge-device-security-amid-rising-cyber-threats
- Cybersecurity and Infrastructure Security Agency. (2026, February 5). Reducing the attack surface for end of support edge devices. https://www.cisa.gov/resources-tools/resources/reducing-attack-surface-end-support-edge-devices
- National Institute of Standards and Technology. (2020). Zero trust architecture (Special Publication 800 207). U.S. Department of Commerce. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-207.pdf
- National Institute of Standards and Technology. (2021). IoT device cybersecurity guidance for the federal government: Establishing IoT device cybersecurity requirements (Special Publication 800 213). U.S. Department of Commerce. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-213.pdf
- U.S. Department of Defense. (2022). DoD Zero Trust Reference Architecture, Version 2.0. Office of the Chief Information Officer. https://dodcio.defense.gov/Portals/0/Documents/Library/%28U%29ZT_RA_v2.0%28U%29_Sep22.pdf
- U.S. Department of Defense. (2022). DoD Zero Trust Strategy. Office of the Chief Information Officer. https://dodcio.defense.gov/Portals/0/Documents/Library/DoD-ZTStrategy.pdf
- U.S. Department of Defense. (2025, November 18). Zero Trust for Operational Technology Activities and Outcomes. Office of the Chief Information Officer. https://dodcio.defense.gov/Portals/0/Documents/Library/ZT-OperationalTechnologyActivitiesOutcomes.pdf

